Mapping Security Risks with Effective Risk Management Strategies
Understanding and mitigating cybersecurity risks before they disrupt operations is no longer optional—it's the foundation of business resilience and...
4 min read
.jpeg) Michael Markulec
:
Jun 10, 2024 2:56:20 PM
Michael Markulec
:
Jun 10, 2024 2:56:20 PM

Discover the key factors and strategies involved in risk assessment within security risk management.
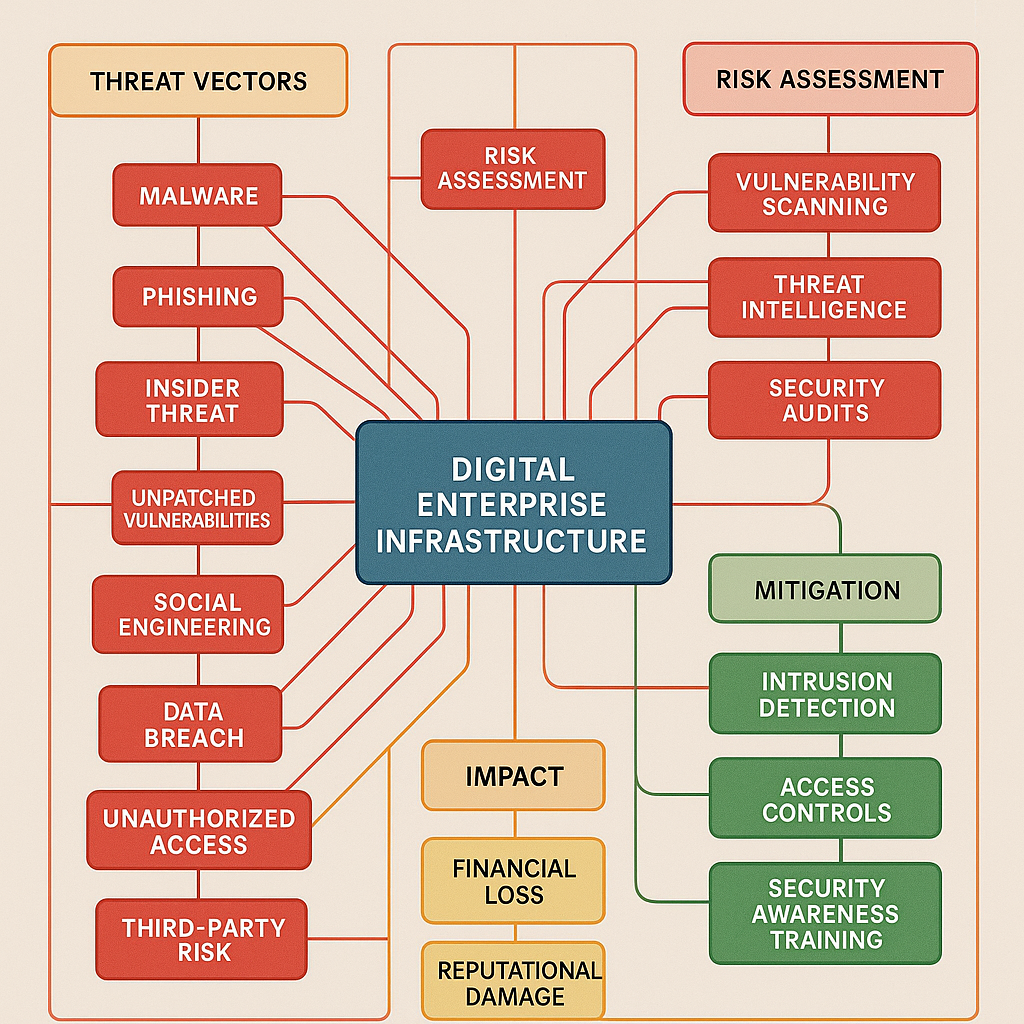
Risk assessment plays a crucial role in security risk management. It involves identifying and evaluating potential risks that could compromise the security of an organization's physical, digital, or intellectual assets. By understanding the role of risk assessment, organizations can proactively implement appropriate security measures to mitigate these risks.
One of the main objectives of risk assessment is to prioritize security efforts and allocate resources effectively. Organizations can identify and assess risks to determine which areas require immediate attention and investment. This ensures that security measures are targeted and tailored to address the most significant threats.
Risk assessment also helps organizations comply with industry regulations and standards. By identifying potential vulnerabilities and assessing the likelihood and impact of possible threats, organizations can implement controls and safeguards to meet compliance requirements.
In summary, risk assessment is a fundamental component of security risk management. It enables organizations to identify and evaluate potential risks, prioritize security efforts, and comply with industry regulations and standards.
A comprehensive risk assessment involves several vital components that help organizations understand their security risks holistically. These components include:
Identifying Assets: This involves identifying and cataloging all valuable assets within an organization, including physical assets such as buildings and equipment and digital assets such as data and software.
Assessing Vulnerabilities: Organizations need to identify and evaluate vulnerabilities that potential threats could exploit. This includes conducting vulnerability scans, penetration tests, and other assessment techniques to identify weaknesses.
Evaluating Threats: Organizations must assess potential threats that could exploit vulnerabilities and cause harm to assets. This involves analyzing external and internal threats, understanding their motivations and capabilities, and evaluating their actions' likelihood and impact.
Analyzing Risks: Once vulnerabilities and threats have been identified, organizations need to analyze the risks associated with each potential scenario. This involves quantifying the likelihood and impact of each risk, considering factors such as the value of assets, the effectiveness of existing controls, and the potential consequences of an incident.
Prioritizing Risks: Based on the analysis of risks, organizations need to prioritize them to focus their resources and efforts effectively. This involves assigning a risk rating to each identified risk and considering factors such as the potential impact, the likelihood of occurrence, and the organization's risk appetite.
Developing Mitigation Strategies: Organizations should develop strategies to mitigate identified risks. This may involve implementing controls and safeguards, creating incident response plans, and establishing monitoring and detection mechanisms.
By considering these key components, organizations can conduct a comprehensive risk assessment that provides valuable insights for security risk management.
Technology is critical in enhancing the effectiveness and efficiency of risk assessment in security risk management. By leveraging technology, organizations can streamline risk assessment and obtain more accurate and timely results.
One way technology can be utilized is through automated risk assessment tools. These tools can help organizations identify vulnerabilities and assess risks more efficiently by automating data collection, analysis, and reporting. They can also provide real-time monitoring and alerting, enabling organizations to respond promptly to emerging threats.
Another technology that can be utilized is artificial intelligence (AI). AI algorithms can analyze large volumes of data to identify patterns, trends, and anomalies that may indicate potential risks. By leveraging AI, organizations can gain deeper insights into security risks and make more informed decisions.
Technology can also facilitate collaboration and information sharing among stakeholders involved in risk assessment. Online platforms and secure communication tools enable effective communication and collaboration, ensuring that all relevant parties can access the necessary information and contribute to the risk assessment process.
In summary, technology offers various opportunities for improving the effectiveness and efficiency of risk assessment in security risk management. Organizations can enhance risk assessment capabilities by utilizing automated tools, AI, and collaboration platforms to make better-informed decisions.
While risk assessment is crucial for effective security risk management, it has its challenges. Risk assessment relies heavily on accurate and up-to-date data. However, organizations may face challenges in collecting and analyzing relevant data, mainly because they operate in complex and dynamic environments.
Risk assessment involves making subjective judgments and assumptions based on available information. Different stakeholders may have different perspectives and risk tolerances, which can make reaching a consensus challenging.
The landscape of security risks is constantly evolving, with new threats emerging regularly. Organizations need to stay updated on the latest trends and technologies to assess and mitigate these emerging threats effectively.
Despite these challenges, there are several best practices that organizations can follow to improve their risk assessment processes. Risk assessment should be an ongoing process rather than a one-time event. Regular assessments help organizations stay updated on evolving risks and ensure their security measures remain effective.
Risk assessment should involve input from various stakeholders, including IT professionals, security experts, legal advisors, and business leaders. This multidisciplinary approach ensures that all relevant perspectives are considered and helps develop comprehensive risk mitigation strategies.
Organizations should continuously learn from risk assessment processes and incorporate lessons learned into future assessments. This iterative approach helps refine risk assessment methodologies and improve security posture.
Addressing challenges and following best practices can enhance the effectiveness and reliability of organizations' risk assessment processes.
Risk assessment in security risk management constantly evolves to keep pace with emerging threats and technological advancements. Several trends are shaping the future of risk assessment:
Big Data Analytics: The increasing availability of large volumes of data presents opportunities for more advanced risk assessment techniques. Big data analytics can help organizations identify patterns, trends, and correlations that may indicate potential risks.
Machine Learning: Machine learning algorithms can analyze vast amounts of data and learn from patterns to identify potential risks. By leveraging machine learning, organizations can automate parts of the risk assessment process and make more accurate predictions.
Threat Intelligence: Threat intelligence, such as information about known threats and their tactics, techniques, and procedures (TTPs), can enhance risk assessment capabilities. Organizations can better understand the evolving threat landscape and prioritize mitigation efforts by integrating threat intelligence into risk assessment processes.
Integration with Cybersecurity: Risk assessment is closely linked to cybersecurity, as many risks involve potential cybersecurity incidents. The integration of risk assessment with cybersecurity technologies and practices can help organizations identify and mitigate cybersecurity risks more effectively.
Real-time Risk Assessment: Traditional risk assessment processes are often conducted periodically. However, the future of risk assessment may involve real-time assessment that continuously monitors and evaluates risks. This enables organizations to respond promptly to emerging threats and reduces the time gap between risk identification and mitigation.
In conclusion, risk assessment in security risk management is evolving to adapt to the changing threat landscape and technological advancements. By embracing trends such as big data analytics, machine learning, threat intelligence, integration with cybersecurity, and real-time assessment, organizations can enhance their risk assessment capabilities and better protect their assets.
Understanding and mitigating cybersecurity risks before they disrupt operations is no longer optional—it's the foundation of business resilience and...

While Managed Service Providers (MSPs) can enhance your business's IT capabilities, it's essential to understand the inherent risks they carry to...

In an age where digital threats loom around every virtual corner, cybersecurity is no longer just a concern for tech giants or governmental bodies....